Enterprise-Grade SSH Security & Monitoring
Protect your critical infrastructure with comprehensive visibility, advanced threat detection, and automated response capabilities.
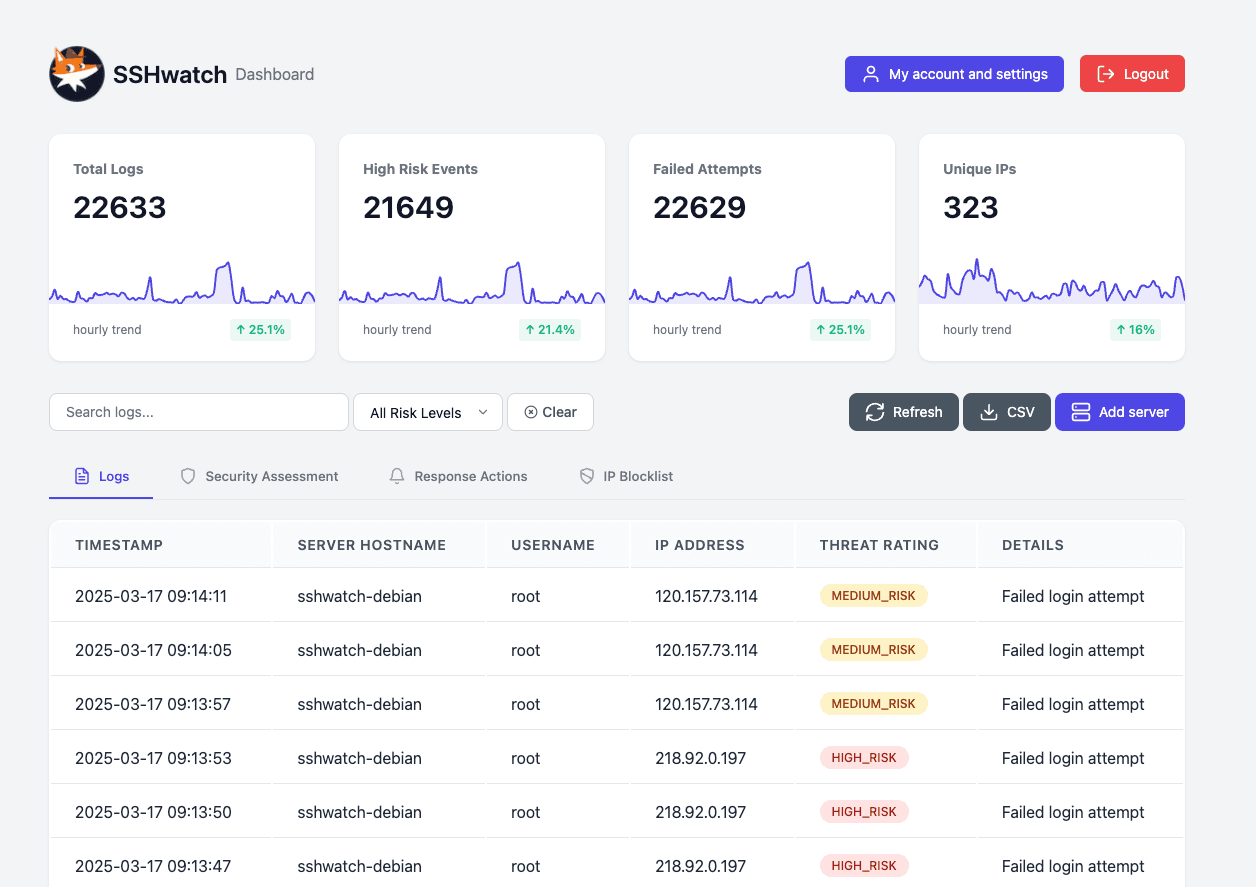
Real-time SSH Monitoring & Threat Detection
Customizable Response Actions
Automated Alerting and Blocklists
Book a demoGet started (free)
"Infrastructure security that scales with your ambition, not against it."
Jennifer Torres, CTO at CloudStream Solutions
"Finally, SSH monitoring that works as hard as your DevOps team does."
Mike Chen, Senior Infrastructure Engineer
"Turn your server logs from overwhelming data into actionable security intelligence."
Emma Beau, VP of Engineering ScaleUp Ventures
Complete access monitoring solution
SSHwatch delivers enterprise-grade security through real-time monitoring, intelligent threat detection, and customizable alert rules. Protect your infrastructure with automated responses to suspicious activities while gathering comprehensive metadata for forensic analysis. Our solution provides deep visibility into user patterns and system events, helping you identify and mitigate potential security breaches before they escalate to serious incidents.
Explore all our featuresSimple and effective dashboard
Transform your security posture with SSHwatch's intuitive dashboard and powerful analytics engine. Monitor SSH activities in real-time while receiving instant alerts about suspicious login attempts and unusual access patterns. Customize security policies based on your organization's requirements and leverage detailed traffic analysis to uncover hidden threats. Our continuous protection ensures your critical infrastructure remains secure 24/7, even against evolving attack vectors.
Go to the dashboardYour Access Security, Simplified
Detect threats in real-time,
respond automatically, and maintain
your advantage with actionable intelligence.

Actionable, log-based security assesments
Log-based security assessments are essential for enhancing your SSH security. Our platform analyzes logs from all Linux-based servers to provide:
With our log-based assessments, you gain the insights needed to proactively manage SSH security threats.
Identifies critical vulnerabilities within your network infrastructure.
Tailored mitigation strategies to address identified security risks.
Continuous monitoring to prevent potential threats from exploiting vulnerabilities.
How to get started
Deploy and Monitor SSH Logs in Minutes
1. get API key
Login to the dashboard to find your API key and installation instructions. We support Debian and RHEL-based systems.
2. install agent
Install the SSHwatch agent on your Linux servers. This agent will send all SSH-related logs to our API.
3. monitor and analyze
All access logs will be available in the dashboard for analytics and custom alerting via email or webhook.
Learn more about how SSHwatch works
From the blog
All articles

SSH Monitoring ROI: Quantifying the Business Value of Visibility into Remote Access
SSH connections are critical for server administration, but they also represent a significant security risk...

SSH, First Line of Defence: Protecting Your Digital Gateway
Every day, millions of login attempts target servers worldwide. Standing guard at the gateway of...

SSH Honeypots: Detecting and Understanding Attack Patterns
SSH servers continue to be prime targets for attackers worldwide, with millions of automated attempts...
